Automate Your Awareness Plan: Mastering Human Cyber-Risk with Kymatio’s Micro-Video Workflow
Scale security awareness automation with Kymatio. Deploy micro-learning workflows, meet NIS2 compliance, and manage human cyber-risk in real-time.

To effectively master Human Risk Management in 2026, organizations must pivot from reactive, manual training to comprehensive security awareness automation driven by specialized Kymatio features. This transition ensures that your "human perimeter" is constantly defended by adaptive workflows while providing the real-time, automated evidence required to satisfy the strict reporting mandates and personal liability requirements of the NIS2 Directive.
The European cybersecurity landscape now operates under a fundamental shift in regulatory and threat dynamics. Standard awareness plans are simply no longer sufficient; you need the automation and key Kymatio features required to counter the velocity of AI-driven social engineering. Empower your security teams by removing the administrative burden of manual scheduling. Scale your defense by reaching every employee with targeted content designed to bridge individual knowledge gaps identified during assessment sessions. Protect your leadership by establishing a comprehensive human risk management strategy that preemptively addresses vulnerabilities to prevent regulatory friction or material data exposure.
Under the weight of current regulations, failing to automate is a risk in itself. High-level stakeholders are now facing the reality of executive legal liability under NIS2, where a lack of demonstrable diligence in training can result in significant personal fines and professional disqualification for the C-suite. Recent data suggests that over 90% of successful breaches still involve a human element, making an automated micro-learning platform with advanced Kymatio features the most critical investment for your 2026 budget.
How to Transition to Automated Human Risk Management
- Map your risk surface: Identify high-risk user groups through initial diagnostic simulations and behavioral analysis.
- Deploy a micro-learning platform: Implement a system that delivers bite-sized content triggered by an assessment performance or seasonal threats.
- Automate evidence collection: Synchronize all training records with your compliance dashboard to ensure you are always audit-ready.
Why Manual Awareness Plans Fail the NIS2 Compliance Test
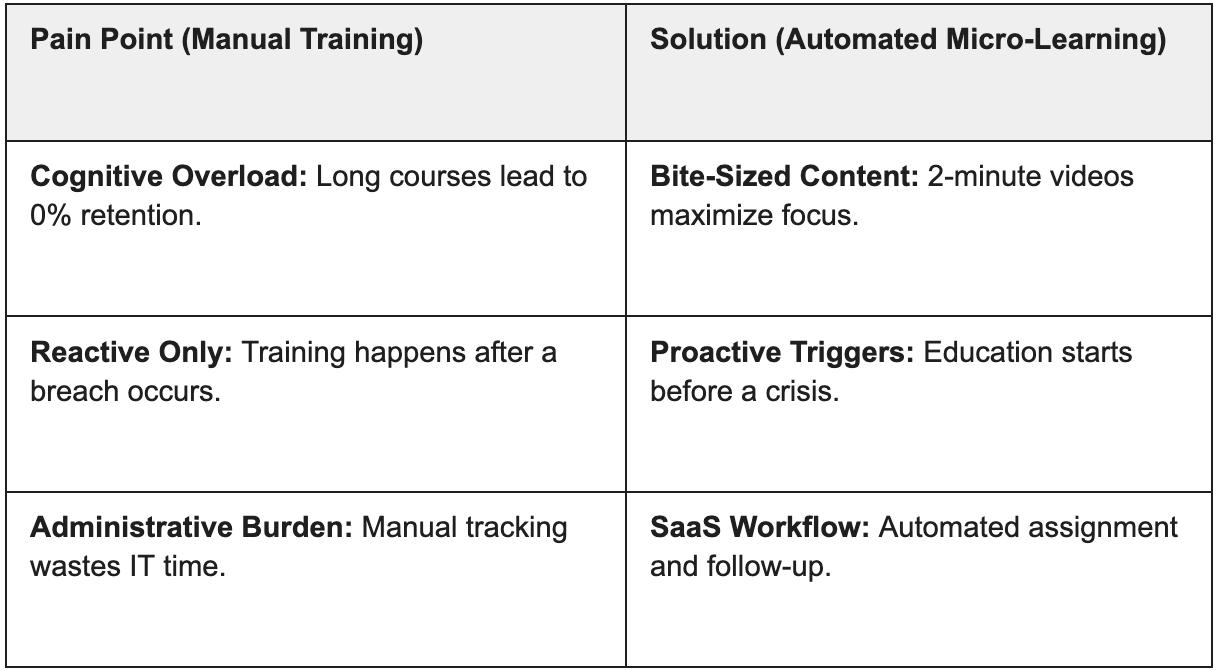
Manual awareness plans fail because they lack the continuity and real-time reporting required to meet the strict "due diligence" standards of the NIS2 Directive. In the 2026 regulatory landscape, static spreadsheets and annual training sessions are insufficient to protect the board from executive liability or to prove a proactive defense posture during a mandatory audit.
The burden of evidence and personal liability
Under the current European cybersecurity regulatory frameworks, compliance is no longer a "check-the-box" exercise. Regulators now demand granular evidence of ongoing training effectiveness and behavioral improvement. Manual management makes it nearly impossible to correlate training with actual risk reduction, leaving the C-suite vulnerable to personal sanctions.
By adopting security awareness automation, organizations eliminate the risk of human error in reporting. Automated workflows ensure that every interaction is logged, providing a tamper-proof audit trail that satisfies the legal requirements for phishing simulations and continuous education mandated by NIS2. According to the ENISA Threat Landscape 2025, the professionalization of social engineering means that a single manual training session per year is effectively obsolete before it even concludes.
Overcoming employee burnout with micro-learning
Traditional 60-minute "death by PowerPoint" sessions lead to cognitive overload and "security fatigue," which significantly raises Human Risk. To solve this, companies are shifting toward a micro-learning platform approach that integrates education into the daily workflow without causing burnout.
Feature Spotlight: The Kymatio Micro-Video Workflow
Kymatio’s Micro-Video Workflow is a specialized security awareness automation engine that identifies specific knowledge vulnerabilities through interactive assessments and immediately triggers hyper-focused, one-minute training sessions. By delivering bite-sized content through this micro-learning platform, specialized Kymatio features ensure maximum information retention and security awareness automation for NIS2 and DORA compliance.
Psychology-Driven Micro-Learning Platform
Traditional training fails because it ignores how the human brain processes stress and information. Kymatio reengineers the training experience by utilizing psychology-based content engineered to overcome cognitive saturation and fragmented employee focus. Instead of overwhelming users with annual 40-minute modules, our platform delivers high-impact, cinematic micro-videos that focus on a single, actionable defense tactic.
This approach is backed by industry research. A recent Gartner study identifies that behavior-focused programs and specialized platforms will reduce employee-driven security incidents by 40% by 2026. By focusing on the why behind the behavior, Kymatio changes long-term habits rather than just ticking a compliance box.
Just-in-Time (JiT) Training Triggers
One of the most powerful Kymatio features is the ability to automate the bridge between a failed simulation and a learning opportunity. This is known as Just-in-Time (JiT) training. When an employee interacts with a simulated threat, the SaaS workflow automatically assigns a relevant video, such as:
- Simulation Interaction: An employee clicks a suspicious link or scans a rogue QR code.
- Automated Trigger: The platform isolates the underlying cognitive trigger (e.g., urgency bias).
- Instant Remediation: The user is immediately presented with a 90-second video explaining how they were targeted.
- Reporting: The system logs the successful completion of the training as audit-ready evidence.
This automated cycle is essential for any integrated attack simulation and awareness guide looking to prove "due diligence" to regulators. It also allows for highly specialized training, such as defending against voice fraud and deepfakes, targeting only the users most susceptible to those specific vectors.
Data-Driven Learning Paths: Automated Knowledge Remediation
Kymatio’s Data-Driven Learning Paths automate the transition from assessment to reinforcement by delivering targeted micro-videos based on specific knowledge gaps identified during user sessions. This ensures that every employee receives personalized content exactly where their understanding is weakest, providing the continuous, documented evidence of "due diligence" required by the NIS2 Directive.
By utilizing psychology-based evaluations, the platform moves beyond generic training to focus on individual needs. Instead of manual scheduling, security awareness automation handles the delivery of content, ensuring that the micro-learning platform remains relevant to each user's specific risk profile. This process is essential for any integrated attack simulation and awareness guide looking to demonstrate a proactive defense posture to regulators.
To maintain a high level of operational efficiency, Kymatio follows a precise four-step automated cycle:
- Interactive Assessment: Employees complete diagnostic sessions that evaluate their understanding of modern threats like AI-phishing or social engineering.
- Gap Identification: The platform isolates the specific topics or cognitive triggers where the user failed to demonstrate proficiency.
- Targeted Video Assignment: The SaaS workflow automatically unlocks a relevant 90-second micro-video pill to reinforce the specific area of weakness.
- Evidence Generation: Every interaction is logged, providing the audit-ready records necessary for defending against voice fraud and deepfakes and other high-stakes vectors.
Architecting the Workflow: How Kymatio Automates the Employee Journey
Kymatio streamlines the employee journey by integrating systematic knowledge assessments with personalized reinforcement through a seamless SaaS workflow. These Kymatio features ensure that when session results identify a specific knowledge gap, security awareness automation delivers targeted content via the micro-learning platform, effectively narrowing the distance between risk identification and educational remediation.
From AI-Phishing Detection to Automated Remediation
Modern security awareness automation must match the rapid evolution and velocity of current cyber threats. By mapping training triggers to the MITRE ATT&CK (Phishing), Kymatio ensures that training reflects the latest industry trends, such as link-based or attachment-heavy tactics.
To achieve a strategic approach to simulated threats, the platform follows a precise four-step automation cycle designed to neutralize knowledge gaps:
- Simulation Deployment: The system launches a campaign based on evolving social engineering tactics like AI-phishing or QRishing.
- Vulnerability Mapping: The SaaS workflow analyzes results from simulations and sessions, flagging specific "at-risk" profiles or topics where knowledge is lacking.
- Automated Content Release: Instead of a generic approach, the platform automatically triggers the release of targeted micro-video pills based on the specific gaps identified during assessment sessions.
- Compliance Data Generation: The system tracks completion and updates the department's risk score, providing the continuous, audit-ready evidence required for NIS2 and DORA compliance.
Customizing Content for Diverse Risk Profiles
Effective Human Risk Management requires collaboration between HR and Security. Kymatio allows you to tailor your training strategy by assigning specific learning paths to different departments based on the specific risk profiles of different departments. While your finance team might be prioritized for vishing and CEO fraud modules, your developers might receive workflows focused on secret leakage or generative AI safety.
Workflow Visualization: Imagine a centralized dashboard where HR directors can see participation velocity while CISOs monitor risk reduction. This dual visibility ensures that training is not just a technical requirement, but a cultural shift that fulfills NIS2’s demand for a "comprehensive management of risk."
Data-Driven Success: KPIs and Audit-Ready Reporting
Through specialized Kymatio features, the platform provides security awareness automation that transforms human risk into actionable data via our micro-learning platform. Through advanced security awareness automation, the platform generates the verifiable evidence needed to prove "due diligence" to auditors and the board, effectively bridging the gap between training participation and actual risk reduction.
Real-time dashboards for the C-Suite
In the current threat landscape, a CISO cannot manage what they cannot measure. Utilizing automated Kymatio features, leadership can visualize the direct ROI of their micro-learning platform and overall security awareness automation efforts. These high-level human risk indicators and dashboards move beyond simple completion rates, focusing instead on behavioral shifts and attack resistance across different departments.
By utilizing these Kymatio features, security leads can identify "high-risk clusters" before a breach occurs. This allows for a surgical reallocation of resources, moving from a broad, generic training approach to a high-precision strategy that targets specific vulnerabilities identified in the SaaS workflow.
Generating compliance evidence automatically
The NIS2 directive mandates that essential and important entities implement and supervise robust risk-management measures. Kymatio simplifies this by automating the collection of compliance evidence for NIS2 audits, creating a tamper-proof trail of every simulation, video viewed, and score improved.

Instead of spending weeks manually compiling spreadsheets for an inspection, administrators can execute instantaneous compliance reporting. This level of automation ensures your organization remains "audit-ready" 365 days a year, not just during the week of an external review.
Frequently Asked Questions


Kymatio generates granular logs, including simulation results, completion timestamps for micro-learning, and behavioral evolution metrics. These serve as technical evidence that an organization is actively managing and mitigating human risk, satisfying the directive's "due diligence" requirements.


NIS2 turns employee awareness into a legal obligation where companies must demonstrate that training is continuous. Staff and senior management must possess the necessary skills to identify and report threats effectively to avoid personal liability.


Kymatio automates the journey by assigning specific micro-videos based on quiz performance. This ensures that employees receive reinforcement exactly where knowledge gaps are identified during their assessment sessions, maintaining a high level of NIS2 compliance.


They translate technical risk by showing a decrease in the organization’s "Human Risk Coefficient" and high "Improvement Rates". This allows CISOs to clearly demonstrate the ROSI of their security awareness automation strategy to the board.


By delivering 1-2 minute high-impact videos, Kymatio respects the "attention economy" and psychological principles of retention. This method results in much higher retention rates compared to traditional long-form courses, focusing on behavioral change.


Yes; all logs and training records are exportable in standardized formats. This ensures you can quickly provide the necessary documentation to pass an inspection or respond to a regulatory inquiry regarding your security culture.









