Designing a Security Awareness Strategy that Convinces the CEO
Master your CISO board presentation. Learn to align your security awareness strategy with NIS2 and use ROSI to secure long-term executive sponsorship.

To secure long-term executive buy-in, your security awareness strategy must evolve from a passive checklist into a proactive Human Risk Management (HRM) framework designed for a modern boardroom strategy. This shift integrates cybersecurity into the core of business resilience that protects company valuation and ensures operational continuity in the face of evolving digital threats.
For years, the C-Suite viewed security training as a "check-the-box" exercise—a yearly nuisance with little measurable impact. However, in the era of NIS2 and DORA, simply delivering annual courses is no longer enough. The Board now demands evidence-based protection. You need a Human Risk Management strategy that treats your employees as a Human Firewall—a measurable, defensive asset as active contributors to the organization’s overall defense-in-depth.
You might ask yourself: "How does this shift affect my CISO board presentation?" It changes the narrative from spending to saving. Instead of talking about phishing click rates, you present a roadmap for reducing the probability of a business-halting breach. By focusing on HRM, you provide the transparency and accountability required by modern regulators and shareholders alike. Treating human risk as a strategic business metric in your boardroom strategy is the only way to move from simple awareness to measurable organizational safety.
Speaking the Board's Language: Risk, Revenue, and ROSI
To secure executive buy-in during a CISO board presentation, your security awareness strategy must translate technical risks into business outcomes like revenue protection and ROSI (Return of Security Investment). Shifting the focus from threat technicalities to financial resilience allows the Board to view cybersecurity as a strategic asset that prevents capital loss rather than a mere operational expense.
The Board of Directors rarely focuses on malware signatures or firewall logs; their primary concerns are EBITDA, market reputation, and regulatory compliance. According to a recent Gartner community report, 61% of CISOs are prioritizing the improvement of metrics and KPIs to better articulate cyber risks to executive leadership. To succeed, your CISO board presentation must bridge the gap between technical vulnerabilities and business impact.
Translating Vulnerabilities into Business Impact
When discussing the "Human Firewall," don't just talk about phishing click rates. Instead, explain how human error directly correlates to business downtime and lost revenue. Under the NIS2 framework, the question isn't just "how does NIS2 affect employee management?" but rather "how does a single employee’s mistake lead to a €10M fine or the disqualification of the CEO?".
By linking human behavior to specific business processes, you demonstrate that a proactive security awareness strategy is the only way to safeguard the company’s valuation. Executives need to see that investing in measuring security culture through data provides the visibility required to prevent catastrophic operational halts.
Calculating the ROSI (Return of Security Investment)
Unlike traditional ROI, where you measure profit generated, ROSI measures the cost of incidents avoided. In a CISO board presentation, this metric serves as the definitive financial evidence for your strategy. It allows you to present the budget not as a "cost," but as a "saving" by reducing the probability of a breach.
To build a compelling case for executive buy-in, use these four financial KPIs to demonstrate value:
- Projected Breach Avoidance Cost: The difference between the average cost of a breach in your sector and the cost of the HRM solution.
- Cyber Insurance Optimization: How a documented, evidence-based culture of security can lead to a reduction in insurance premiums.
- Regulatory Penalty Avoidance: Quantifying the potential fines under NIS2 (up to 2% of global turnover) that are mitigated by compliant behavior.
- Operational Resilience Ratio: The reduction in help-desk hours and incident response resources due to fewer successful social engineering attacks.
Asking "what tools do I need to assess digital human risk?" is the first step toward a data-driven dialogue with the Board. By using ROSI, you transform cybersecurity from a "necessary evil" into a competitive advantage that ensures the organization remains robust, compliant, and profitable.
The NIS2 and DORA Mandate: Why Executive Sponsorship is Mandatory
Under the NIS2 Directive and DORA, executive sponsorship for a comprehensive security awareness strategy is no longer optional—it is almost a mandatory legal requirement. Management bodies are now personally liable for their organization's cyber risk management, meaning a comprehensive security awareness strategy is the primary defense against heavy fines, legal sanctions, and professional disqualification.
For the first time, the "I didn't know" defense is legally dead. Regulators in Spain and across Europe are moving from a "check-the-box" mentality to a "responsibility-centered" framework. In your next CISO board presentation, the focus must shift from technical metrics to a boardroom strategy that addresses how the organization protects its most volatile asset: the human factor.
Article 21 and CEO Personal Liability
One of the most critical aspects of NIS2 compliance is Article 21, which explicitly requires management bodies to approve and oversee cybersecurity risk-management measures. This includes mandatory awareness and hygiene practices for all employees, including the executives themselves.
Failure to implement an effective security awareness strategy and secure executive sponsorship can now lead to personal management liability under NIS2. This means that beyond corporate fines, individual executives could face temporary bans from management functions or personal financial penalties. When the Board asks, "how does NIS2 affect employee management?", the answer is clear: the Board is now legally responsible for ensuring that every stakeholder is equipped to defend the organization against phishing and social engineering.
Regulatory Alert: NIS2 Sanctions in Europe
- Financial Penalties: Essential entities can face fines of up to €10 million or 2% of their total worldwide annual turnover.
- Management Liability: National authorities can hold individual executives personally responsible for gross negligence in risk management.
- Operational Impact: Regulators have the power to suspend management functions and order audits to verify compliance evidence.
Moving Toward Evidence-Based Compliance
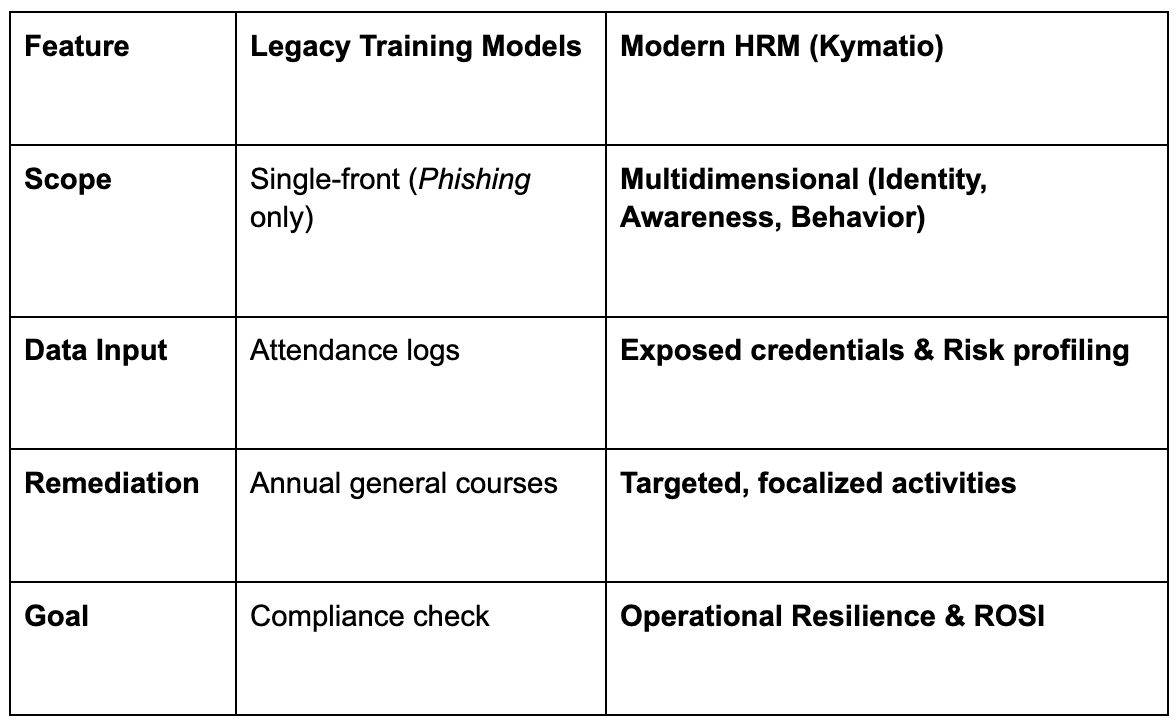
A common pitfall in obtaining executive buy-in is presenting "attendance logs" as proof of safety. In the eyes of an auditor or a court, a signed list of people who watched a video is not evidence of a reduced risk profile. To achieve true NIS2 compliance, organizations must move toward evidence-based results.
- Continuous Simulation Data: Use real-time data from simulated phishing attacks to prove behavioral improvement.
- Behavioral Metrics: Move beyond completion rates to focus on how quickly employees report threats.
- Executive Training: Board members must participate in specialized training to lead by example.
By providing a NIS2 compliance guide for executives, you empower the C-Suite to move from a position of risk to a position of leadership. A proactive security awareness strategy isn't just about training; it is the cornerstone of a resilient and legally sound organization.
Continuous Assessment: Identifying and Closing the Human Capability Gap
To secure executive buy-in, your security awareness strategy must move beyond periodic phishing tests. A sustainable security culture is built on continuous, multidimensional assessment—integrating data from attack simulations, exposed credentials (identity risk), and behavioral psychology to identify and close specific knowledge gaps.
A sustainable security culture requires an executive sponsorship model that replaces passive training with active behavioral change, a core pillar of a robust security awareness strategy. Moving beyond theoretical "classes" to real-world practice allows organizations to strengthen their Human Firewall, ensuring that a security awareness strategy delivers measurable risk reduction rather than just a certificate of completion.
The data supports this shift: the Verizon Data Breach Investigations Report (DBIR) 2025 confirms that the human element—including errors, social engineering, and misuse—remains a critical factor in 60% of all global data breaches. To address this in your next CISO board presentation, you must demonstrate how you are evolving from static content to an active defense posture.
The Power of Targeted Phishing and Vishing Simulations
Traditional training often fails because it happens in a vacuum. In contrast, active simulation puts your team in the driver’s seat of a controlled attack. By deploying safe, targeted phishing, smishing and vishing scenarios, you can identify specific vulnerabilities within different departments before a real threat actor exploits them.
This 'learning by doing' approach transforms employees from potential liabilities into an active Human Firewall, a critical asset for operational resilience under the Zero Trust paradigm. When people experience the nuances of a sophisticated attack in a safe environment, they develop the "muscle memory" needed to spot anomalies in their daily workflow. This level of readiness is exactly what secures executive buy-in, as it provides the Board with proof that the workforce is genuinely prepared.
From Passive Content to Behavioral Change
If you are wondering, "what tools do I need to assess digital human risk?", the answer lies in cyberpsychology and data. Passive videos and slides do not change habits; individualized, behavior-based security simulations do.
By analyzing how different profiles react to stressors or psychological triggers, you can tailor the training to the individual. This transition is the core of modern Human Risk Management (HRM):
- Traditional Training: Linear, generic, and often perceived as a "waste of time" by staff.
- Modern Security Culture: Adaptive, gamified, and integrated into the employee's routine.
Ultimately, a culture that rewards reporting and values security as a shared responsibility is far more resilient than one that simply punishes mistakes. By focusing on behavioral change, you move the needle from "knowing" to "doing," creating a long-term defense strategy that stands up to the scrutiny of both regulators and the Board.
Beyond Practical Drills: Assessing Knowledge and Sentiment
A true Human Risk Management (HRM) approach identifies risks that a simple email simulation might miss. This includes monitoring for exposed credentials on the dark web and evaluating the "awareness gap" through neuropsychological profiling. By understanding why a specific department is prone to risk—whether due to lack of knowledge or dangerous workplace habits—you can move from generic training to a surgical defense posture.
Targeted Remediation: Closing the Gap in the Daily Workflow
Once a risk is detected—such as poor password hygiene or neglect of secure workplace behaviors—the HRM platform triggers targeted remediation activities. Instead of overwhelming the entire company, you deploy focused interventions specifically designed for the groups at risk. This precision optimizes capital allocation and ensures that your executive sponsorship translates into measurable behavioral change.
The CISO Board Presentation: A Step-by-Step Blueprint
To deliver a successful CISO board presentation that wins executive buy-in, you must shift the narrative from technical vulnerabilities to business impact and financial resilience. By presenting a data-driven roadmap for your security awareness strategy, you can bridge the gap between human risk and NIS2 compliance, effectively securing the executive buy-in needed for a long-term boardroom strategy.
The Board’s primary concern is not the number of malware blocks, but the continuity of the business. When preparing your pitch, remember that a proactive approach is always more convincing than a reactive one. You are not just asking for a budget; you are proposing a shield for the company’s valuation and a safeguard against personal liability under new European regulations.
Visualizing Human Risk with Real-Time Dashboards
Executives value transparency and actionable data. Move away from static Powerpoint slides and embrace real-time dashboards that show the current state of your organization's Human Firewall. Visualizing risk levels across different departments allows the Board to see exactly where the organization is vulnerable to social engineering or phishing attacks.
This clarity is essential when addressing the question: "What tools do I need to assess digital human risk?". By demonstrating a platform that quantifies behavioral change, you prove that your security awareness strategy is a measurable science, not a guessing game. Highlighting these metrics is the most direct path to obtaining the executive buy-in required to scale your defenses.
In a ciso board presentation, clarity is your strongest currency. Don't just present phishing click rates; present a Holistic Human Risk Matrix. Show the Board how exposed credentials and weak awareness levels in critical departments (like Finance or Legal) create financial exposure. Visualizing the correlation between identity risk and behavioral gaps provides the "smoking gun" needed to justify a robust boardroom strategy.
Establishing the Roadmap for Executive Sponsorship
Secure executive buy-in by showing exactly how you will spend the budget. Your roadmap should move from "Detection" (identifying high-risk profiles) to "Targeted Remediation." Explain that by focusing resources on the 10% of employees responsible for 90% of the risk—whether through credential cleanup or workplace behavior drills—you are maximizing the ROSI and protecting the bottom line.
Use this 5-point checklist to structure your next boardroom pitch:
- Align with Fiduciary Duty: Frame NIS2 compliance as a legal obligation to manage multidimensional risk.
- Highlight Identity Risk: Present data on exposed credentials to show immediate, tangible threats.
- Define the Awareness Gap: Use psychological profiling to explain why certain risks persist beyond technical fixes.
- Propose Targeted Remediation: Show how the security awareness strategy will deploy specific activities for specific risk groups.
- Quantify ROSI: Demonstrate how closing these specific gaps reduces the organization’s overall financial exposure.
By following this blueprint, you transform the CISO board presentation from a technical report into a strategic dialogue. This alignment ensures that the Board views cybersecurity as an investment in the company’s future, rather than just another operational expense.
Conclusion: Making Security a Competitive Advantage
To transform your security awareness strategy into a competitive edge, you must align human resilience with business growth through a proactive Human Risk Management (HRM) approach. This shift not only ensures NIS2 compliance but also creates a culture where every stakeholder acts as a strategic defense layer, protecting both company reputation and long-term financial stability.
Moving from a focus on risk to a focus on resilience creates a brand that stakeholders, partners, and customers can trust. According to the 2025 Verizon DBIR, the human element—including social engineering and error—remains a factor in 60% of all global breaches. Consequently, a verified Human Firewall is no longer just a security measure; it is a vital market differentiator that proves your organization is prepared for the complexities of the modern digital landscape.
If you are asking yourself, "how can I effectively implement this?", follow these three essential steps to solidify your executive buy-in:
- Quantify the Impact: Use ROSI metrics in every CISO board presentation to show the financial value of avoided incidents.
- Automate Compliance: Leverage tools that provide continuous, audit-ready evidence for NIS2 and DORA.
- Empower Behavior: Transition from annual "check-the-box" training to continuous, data-driven simulation and training.
Ultimately, the goal is to stop viewing employees as a liability and start seeing them as your most powerful defensive asset. By implementing a Human Risk Management strategy, you ensure your organization doesn’t just survive the next threat—it thrives.
Frequently Asked Questions


Secure executive buy-in by aligning your strategy with business objectives. Use financial metrics like ROSI and highlight the personal liability risks introduced by the NIS2 Directive to demonstrate that security is a business-critical priority.


Executive sponsorship is essential for shifting corporate culture. When leadership actively supports a boardroom strategy for security, it ensures cross-departmental cooperation, prioritizes budget allocation, and validates the importance of a strong Human Firewall across the organization.


NIS2 Article 21 requires organizations to implement risk-management measures, including security hygiene and awareness. Because management bodies are now legally responsible for these measures, a proactive security awareness strategy is a mandatory tool for regulatory protection.


Focus on ROSI, the percentage reduction in "high-risk" behavior groups, and your progress toward NIS2/DORA alignment. Use data from simulations to show the tangible reduction in the probability of a successful breach.


Traditional training is a passive, one-size-fits-all annual event. Human Risk Management (HRM) is a continuous, data-driven approach that uses simulations and personalized active training to measure and change actual behaviors, creating a resilient security culture.


OSI (Return of Security Investment) quantifies the financial value of avoided risks. It allows the CEO to see cybersecurity not as a sunk cost, but as an investment that protects the company's bottom line from the catastrophic costs of data breaches.









